Ensuring the availability and security of your data and infrastructure is critical.
Yet keeping up with digital transformation, cyberattacks, cloud technologies, and shifting regulatory compliance can be difficult — especially while focusing attention on business strategy and driving innovation.
Ntirety is your answer to this challenge
Secure, Available, Compliant: Ntirety’s Commitment for Mission-Critical Data
At Ntirety, we manage and secure your mission-critical data to support the “entirety” of your environment. We are the one partner who can bring technical competency, strategic guidance, and a commitment to better business outcomes for our customers.

Ntirety Recognized on CRN’s 2024 MSP 500 List
The prestigious Managed Security 100 recognizes industry-leading service providers in North America who are driving a new wave of growth and innovation for the channel through forward-thinking approaches to managed services, helping end users increase efficiency and simplify IT solutions, while maximizing their return on investment.
Go Further with Ntirety
25+ Years of Experience
2,500+ Enterprise Customers
650+ IT and Security Certifications
24x7x365 Security and Network Operations Centers
1.8M Average Attacks Blocked Monthly
0 Breaches for Fully Ntirety-Secured Environments
Certified Expertise
Our team lives and breathes IT, data, security, and compliance, boasting over 650+ top technical certifications … and counting.
-
ARCHITECTURE
- Microsoft Gold Certified
- AWS Architecture, DevOps
- Azure Architecture, DevOps
- VMware
- RedHat
-
SECURITY
- Palo Alto
- Ethical Hacker
- CompTIA Security
-
DATABASES
- Oracle
- MS SQL
- Power BI
- MySQL
- PostgreSQL
-
OPTIMIZATION
- AWS Well-Architected Certification
-
COMPLIANCE
- PCI
- SOC
- HIPAA/HITRUST
- GDPR
- ISO
Awards and Recognition
Compliance Certifications and Attestations







Why Ntirety?
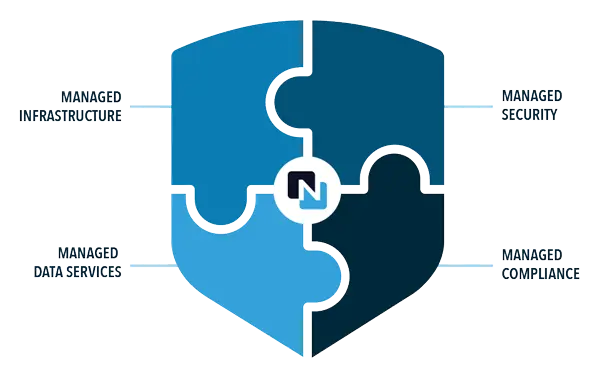
Navigating the complex world of IT can be daunting, especially with limited resources and the mission-critical need for data security. That’s where Ntirety excels. For over 25 years, we’ve been offering robust solutions in managed infrastructure, security, data services, and compliance. Our expert team is dedicated to securing your data and cloud infrastructure, and managing your IT environment, with a focus on continuous business improvement. With personalized support and a partnership approach, we are here to empower your business. Get started today and let us be your trusted partner in the digital world.
Get Started






